User:Jackbelshe/sandbox
In cryptography, encryption is the process of encoding information.[1] This process converts the original representation of the information, known as plaintext, into an alternative form known as ciphertext.[1] Only authorized parties can decipher a ciphertext back to plaintext and access the original information.[1] Historically, various forms of encryption have been used to aid in cryptography. Early encryption techniques were often utilized in military messaging. Since then, new techniques have emerged and become commonplace in all areas of modern computing.[2] Modern encryption schemes utilize the concepts of public-key and symmetric-key.[2] Modern encryption techniques ensure security because modern computers are inefficient at cracking the encryption. However, researchers at NIST and other cybersecurity experts suggest that the development of quantum computers may threaten current encryption systems.[3]
History
[edit]Ancient
[edit]One of the earliest forms of encryption is symbol replacement, which was first found in the tomb of Khnumhotep II, who lived in 1900 B.C. Egypt. Symbol replacement encryption is “non-standard,” which means that the symbols require a cipher or key to understand. This type of early encryption was used throughout Ancient Greece and Rome for military purposes.[4] One of the most famous military encryption developments was the Caesar Cipher, which was a system in which a letter in normal text is shifted down a fixed number of positions down the alphabet to get the encoded letter. A message encoded with this type of encryption could be decoded with the fixed number on the Caesar Cipher.[5]
Around 800 A.D., Arab mathematician Al-Kindi developed the technique of frequency analysis - which was an attempt to systematically crack Caesar ciphers.[4] This technique looked at the frequency of letters in the encrypted message to determine the appropriate shift. This technique was rendered ineffective after the creation of the Polyalphabetic cipher by Leone Alberti in 1465, which incorporated different sets of languages. In order for frequency analysis to be useful, the person trying to decrypt the message would need to know which language the sender chose.[4]
19th-20th Century
[edit]Around 1790, Thomas Jefferson theorized a cipher to encode and decode messages in order to provide a more secure way of military correspondence. The cipher, known today as the Wheel Cipher or the Jefferson Disk, although never actually built, was theorized as a spool that could jumble an English message up to 36 characters. The message could be decrypted by plugging in the jumbled message to a receiver with an identical cipher. [6]
A similar device to the Jefferson Disk, the M-94, was developed in 1917 independently by US Army Major Joseph Mauborne. This device was used in U.S. military communications until 1942.[7]
In World War II, the Axis powers used a more advanced version of the M-94 called the Enigma Machine. The Enigma Machine was more complex because unlike the Jefferson Wheel and the M-94, each day the jumble of letters switched to a completely new combination. Each day’s combination was only known by the Axis, so many thought the only way to break the code would be to try over 17,000 combinations within 24 hours.[8] The Allies used computing power to severely limit the amount of reasonable combinations they needed to check every day, leading to the breaking of the Enigma Machine.
Modern
[edit]Today, encryption is used in the transfer of communication over the Internet for security and commerce.[2] As computing power continues to increase, computer encryption is constantly evolving to prevent attacks.[9]
Encryption in Cryptography
[edit]In the context of cryptography, encryption serves as a mechanism to ensure confidentiality.[2] Since data may be visible on the Internet, sensitive information such as passwords and personal communication may be exposed to potential interceptors.[2] To protect this information, encryption algorithms convert plaintext into ciphertext to transform the original data to a non-readable format accessible only to authorized parties who can decrypt the data back to a readable format.[1]
The process of encrypting and decrypting messages involves keys. The two main types of keys in cryptographic systems are symmetric-key and public-key (also known as asymmetric-key).[1]
Types
[edit]Symmetric Key
[edit]In symmetric-key schemes,[10] the encryption and decryption keys are the same. Communicating parties must have the same key in order to achieve secure communication. The German Enigma Machine utilized a new symmetric-key each day for encoding and decoding messages.
Public Key
[edit]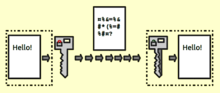
In public-key encryption schemes, the encryption key is published for anyone to use and encrypt messages. However, only the receiving party has access to the decryption key that enables messages to be read.[11] Public-key encryption was first described in a secret document in 1973;[12] beforehand, all encryption schemes were symmetric-key (also called private-key).[13]: 478 Although published subsequently, the work of Diffie and Hellman was published in a journal with a large readership, and the value of the methodology was explicitly described.[14] The method became known as the Diffie Hellman key exchange.
RSA (Rivest–Shamir–Adleman) is another notable public-key cryptosystem. Created in 1977, it is still used today for applications involving digital signatures.[15] Using number theory, the RSA algorithm selects two prime numbers, which help generate both the encryption and decryption keys.[15]
A publicly available public-key encryption application called Pretty Good Privacy (PGP) was written in 1991 by Phil Zimmermann, and distributed free of charge with source code. PGP was purchased by Symantec in 2010 and is regularly updated.[16]
Limitations
[edit]Encryption is used in the 21st century to protect digital data and information systems. As computing power increased over the years, encryption technology has only become more advanced and secure. However, this advancement in technology has also exposed a potential limitation of today’s encryption methods.
The length of the encryption key is an indicator of the strength of the encryption method.[1] For example, the original encryption key, DES (Data Encryption Standard), was 56 bits, meaning it had 256 combination possibilities. With today’s computing power, a 56-bit key is no longer secure, being vulnerable to hacking by brute force attack.[1] Today the standard of modern encryption keys is up to 2048 bit with the RSA system.[17] Decrypting a 2048 bit encryption key is nearly impossible in light of the number of possible combinations. However, quantum computing is threatening to change this secure nature.
Quantum computing utilizes properties of quantum mechanics in order to process large amounts of data simultaneously. Quantum computing has been found to achieve computing speeds thousands of times faster than today’s super computers.[15] This computing power presents a challenge to today’s encryption technology. For example, RSA encryption utilizes the multiplication of very large prime numbers to create a semiprime number for its public key. Decoding this key without its private key requires this semiprime number to be factored, which can take a very long time to do with modern computers. It would take a super computer anywhere between weeks to months to factor this key.[15]
However, quantum computing can use quantum algorithms to factor this semiprime number in the same amount of time it takes for normal computers to generate it.[1] This would make all data protected by current public-key encryption vulnerable to quantum computing attacks. Other encryption techniques like elliptic curve cryptography and symmetric key encryption are also vulnerable to quantum computing.[1]
While quantum computing could be a threat to encryption security in the future, quantum computing as it currently stands is still very limited. Quantum computing currently is not commercially available, cannot handle large amounts of code, and only exists as computational devices, not computers.[18] Furthermore, quantum computing advancements will be able to be utilized in favor of encryption as well. The National Security Agency (NSA) is currently preparing post-quantum encryption standards for the future.[15] Quantum encryption promises a level of security that will be able to counter the threat of quantum computing.[18]
References
[edit]- ^ a b c d e f g h i Agrawal, Monika (May 5, 2012). "A Comparative Survey on Symmetric Key Encryption Techniques". International Journal on Computer Science and Engineering. 4: 877–882.
- ^ a b c d e Kessler, Gary (November 17, 2006). "An Overview of Cryptography". Princeton University.
- ^ Mavroeidis, Vasileios (March 31, 2018). "The Impact of Quantum Computing on Present Cryptography" (PDF). International Journal of Advanced Computer Science and Applications. 9: 1–10.
- ^ a b c "History of Cryptography". Binance Academy. Retrieved 2020-04-02.
- ^ "Caesar Cipher in Cryptography". GeeksforGeeks. 2016-06-02. Retrieved 2020-04-02.
- ^ "Wheel Cipher". www.monticello.org. Retrieved 2020-04-02.
- ^ "M-94". www.cryptomuseum.com. Retrieved 2020-04-02.
- ^ Hern, Alex (2014-11-14). "How did the Enigma machine work?". The Guardian. ISSN 0261-3077. Retrieved 2020-04-02.
- ^ Unisys, Dr Glen E. Newton (2013-05-07). "The Evolution of Encryption". Wired. ISSN 1059-1028. Retrieved 2020-04-02.
- ^ "Symmetric-key encryption software".
- ^ Bellare, Mihir. "Public-Key Encryption in a Multi-user Setting: Security Proofs and Improvements." Springer Berlin Heidelberg, 2000. Page 1.
- ^ "Public-Key Encryption - how GCHQ got there first!". gchq.gov.uk. Archived from the original on May 19, 2010.
- ^ Goldreich, Oded. Foundations of Cryptography: Volume 2, Basic Applications. Vol. 2. Cambridge university press, 2004.
- ^ Diffie, Whitfield; Hellman, Martin (1976), New directions in cryptography, vol. 22, IEEE transactions on Information Theory, pp. 644–654
- ^ a b c d e Wahid, Mohammed Nazeh Abdul; Ali, Abdulrahman; Esparham, Babak; Marwan, Mohamed (2018-08-10). "A Comparison of Cryptographic Algorithms: DES, 3DES, AES, RSA and Blowfish for Guessing Attacks Prevention". Journal of Computer Science Applications and Information Technology. 3 (2). Cite error: The named reference ":2" was defined multiple times with different content (see the help page).
- ^ Kirk, Jeremy (April 29, 2010). "Symantec buys encryption specialist PGP for $300M". Computerworld.
- ^ arXiv, Emerging Technology from the. "How a quantum computer could break 2048-bit RSA encryption in 8 hours". MIT Technology Review. Retrieved 2020-04-02.
- ^ a b Solenov, Dmitry; Brieler, Jay; Scherrer, Jeffrey F. (2018). "The Potential of Quantum Computing and Machine Learning to Advance Clinical Research and Change the Practice of Medicine". Missouri Medicine. 115 (5): 463–467. ISSN 0026-6620. PMC 6205278. PMID 30385997.
 | This is a user sandbox of Jackbelshe. You can use it for testing or practicing edits. This is not the sandbox where you should draft your assigned article for a dashboard.wikiedu.org course. To find the right sandbox for your assignment, visit your Dashboard course page and follow the Sandbox Draft link for your assigned article in the My Articles section. |
