User:Bdmparker/Cyber security awareness
| This is the sandbox page where you will draft your initial Wikipedia contribution.
If you're starting a new article, you can develop it here until it's ready to go live. If you're working on improvements to an existing article, copy only one section at a time of the article to this sandbox to work on, and be sure to use an edit summary linking to the article you copied from. Do not copy over the entire article. You can find additional instructions here. Remember to save your work regularly using the "Publish page" button. (It just means 'save'; it will still be in the sandbox.) You can add bold formatting to your additions to differentiate them from existing content. |
Article Draft
[edit]Lead
[edit]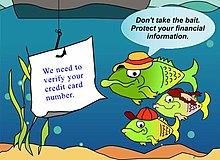
Cyber security awareness refers to how much end-users know about the cyber security threats their networks face, the risks they introduce[1] and mitigating security best practices to guide their behavior.[2] End users are considered the weakest link and the primary vulnerability within a network.[2][3][4] Since end-users are a major vulnerability, technical means to improve security are not enough: organizations must also provide security best practice guidance for end users' awareness of cyber security. They should teach employees about common threats and how to avoid or mitigate them.[4]
Article body
[edit]Approach
[edit]A cyber security end user program could include a combination of multiple approaches consisting of cyber security awareness, cyber security training, and cyber security education. According to [2], see the below table that provides a comparison of the approaches.
| AWARENESS | TRAINING | EDUCATION | |
| Attribute | “What” | “How” | “Why” |
| Level | Information | Knowledge | Insight |
| Objective | Recognition | Skill | Understanding |
| Delivery Method | Media
Including: video, newsletters, posters |
Practical Instruction Including: lecture, case study workshop, hands-on | Theoretical Instruction Including: discussion seminar, background reading |
| Impact Timeframe | Short-term | Intermediate | Long-term |
Threats
[edit]Threat agents or threat actors are the perpetrators of the threat and usually look for the easiest way to gain access into a network, which is often the human element.[5] However, these cyber threats can be mitigated.[6] Some common threats include but are not limited to below.
Social engineering is when someone uses a compelling story, authority, or other means to convince someone to hand over sensitive information such as usernames and passwords.[7][8] An end user with cyber security awareness will have the ability to recognize these types of attacks and avoid them.
Phishing is a form of social engineering.[9] It is a popular attack that attempts to trick users into clicking a link within an email or on a website in hopes that they divulge sensitive information. This attack generally relies on a bulk email approach and the low cost of sending phishing emails. Few targets are fooled, but so many are targeted that this is still a profitable vector.
Spear phishing is an email crafted and sent to a specific person to whom it may appear to be legitimate.[10] It is a form of phishing, but it is more convincing and more likely to succeed than traditional phishing emails because it tailors the email to the victim. Its deployment can range from a bulk automated process, such as accessing the address book of a past victim and sending simple phishing attacks to their contacts, coming from a recognised past contact, to more sophisticatedly hand-written communications to target specific recipients.
Vishing or voice phishing is a form of social engineering [9] that involves contacting individuals via traditional landlines, telephony (i.e., Voice over IP), automated text-to-speech systems, or other forms of voice communications to trick them into divulging sensitive information like credit card data. (Griffin).
Smishing or SMS phishing is social engineering [9] that leverages SMS or text messages as the vector to trick end users into divulging sensitive information.
Tailgaiting is a physical security social engineering attack in which an unauthorized individual can access a location by following an authorized user into the location without the authorized user's knowledge.[11]
Piggybacking is a physical security social engineering attack in which an unauthorized individual can access a location by following an authorized user into the location with the authorized user's knowledge.[11]
Malware is software created and used for malicious intent. It includes a range of software to include but is not limited to viruses, trojan horses, worms, rootkits, spyware, and crypto-jacking.[12]
Ransomware is another cyber threat where attacks are carried out on the computer system but are often the result of a social engineering attack.[13][14] This type of malware encrypts data and holds it for ransom which could paralyze the whole computer system.
Internet of Things (IoT) based attacks are a form of cyber threat in the 21st century and beyond that leverage embedded devices in, i.e., cars, refrigerators, and smartphones.
Topics
[edit]These topics are relevant to cyber security awareness, cybersecurity training, and cyber security education. As reflected in the above table, there are several different approaches that can be taken to provide cyber security awareness.[4] Some of which include using posters, guides, tips [15] or even video and newsletters [2]. Some possible Cyber security awareness topics according to [16][17][18] include but are not limited to the following.
Anti-Malware Protection: Anti-malware is sometimes referred to as anti-virus. This type of application is used to protect systems against malicious software by preventing, detecting, and deleting malicious software. Some popular malware includes computer viruses, ransomware, rootkit, trojan horses, and worms. Security end user awareness guidelines include device scans for malware and updating the anti-malware application definitions.[16]
Data Protection and Privacy: There are various types of data that might be mandated to be protected from unauthorized disclosure, including personally identifiable information (PII), protected health information (PHI), intellectual property (IP), and other sensitive information. Security awareness guidelines include teaching related to data classification, encryption, data anonymization, and data masking or data obfuscation. Permissions and who can access data, which includes file sharing via email attachments, are additional safeguards that could be discussed. Another data protection control that could be included is backing up data [16] as it could be restored if the original becomes unavailable.
Device Management: involves knowing how to protect mobile devices and computers. Device Management is also concerned with security related to Bring Your Own Device (BYOD). Security awareness guidelines include encryption, protecting the system with a password, PIN, or multi-factor authentication, and other forms of credential. Additional awareness tips include end-users downloading, installing, and reviewing applications and the requested permissions from unknown sources.[17][19] According to [17], another awareness tip is to read reviews and comments about the application before installing it. Additionally, the use of public WIFI is another discussion point.[17] Device management also relates to maintaining an accurate inventory of assets from purchase to disposition. This includes knowing when to wipe a device and media sanitization.
Incident Response: An incident is any observable event of malicious intent. Security awareness guidelines for end-users include what types of events are considered suspicious or malicious, who should be contacted if an incident occurs, and what actions should be taken in the event of an incident.[16]
Internet of Things Security: are remotely controlled capable, resource constrained devices with embedded sensor chips that interact with people and objects to collect data and provide it to remote sources on the Internet for additional analysis in an effort to personalize and customize a user's experience. These devices include but are not limited to smart speakers, wearable devices like smart watch, surveillance cameras, lights, door locks, thermostats, appliances and cars. Guidelines include maintaining an asset inventory, patch control, and change default credentials.[20]
Password Management: A password is a string of secret characters used to authenticate a user's account. Security awareness guidelines suggest presenting requirements for creating a strong password or Passphrase, how frequently passwords should be changed, and how to protect passwords.[16] Additionally, guidelines suggest the need to change all default passwords and to not share passwords with others.[21] Additional protection options could include making end-users aware of using multi-factor authentication, password managers, and awareness of various password-related threats like password cracking.
Patching: Software and system changes to update, improve, or resolve weaknesses are usually released via a patch. Security awareness guidelines include the timely installation of security patches [16] as well as implementing vulnerability assessment and vulnerability management.
Removable Media: are storage devices that could be added or removed from a running computer, such as CDs, DVDs, removable SD cards, and USB drives (including flash drives, thumb drives, external hard drives). Security awareness guidelines include drive encryption, following the policy and guidelines presented at the organizational level regarding the use of personal devices on organizational systems.[21]
Safe Web Browsing: Security awareness guidelines regarding securely navigating websites include looking for the padlock icon on the URL bar before entering sensitive information like credentials, credit card information, or personally identifiable information.[17] Another visual indicator is "https" reflecting in the web address.[17] The padlock and the https mentions indicate that the entered information will be secure.[17] Lastly, guidance could be shared to set privacy options on the browser or use the incognito option to limit the information shared or consider using a virtual private network (VPN)).[22]
Social Engineering involves interacting with humans in hopes that they will disclose sensitive information. (CISA) Security awareness guidelines include not opening suspicious emails from unrecognized senders, not clicking on suspicious links in emails or on websites, not opening attachments in emails, not disclosing information, and not responding to suspicious emails or contacts provided therein..[16][21]
References
[edit]- ^ Kim, Lee (April 2017). "Cybersecurity awareness: Protecting data and patients". Nursing Management. 48 (4): 16–19. doi:10.1097/01.NUMA.0000514066.30572.f3. ISSN 0744-6314.
- ^ a b c d "NIST SP 800-12: Chapter 13: Awareness, Training and Education". csrc.nist.rip.
{{cite web}}: CS1 maint: url-status (link) - ^ "Improving employees' cyber security awareness". Computer Fraud & Security. 2019 (8): 11–14. 2019-08-01. doi:10.1016/S1361-3723(19)30085-5. ISSN 1361-3723.
- ^ a b c "What is Cybersecurity Awareness Training & Why is it so Important?". FraudWatch International. 2018-12-21.
{{cite web}}: CS1 maint: url-status (link) - ^ Abawajy, Jemal (2014-03-04). "User preference of cyber security awareness delivery methods". Behaviour & Information Technology. 33 (3): 237–248. doi:10.1080/0144929X.2012.708787. ISSN 0144-929X.
- ^ "Top 10 Cyber Security Threats & Its Mitigation". vCloud Tech Blogs - Your IT Solutions & Servicers Provider. 2020-11-23.
{{cite web}}: CS1 maint: url-status (link) - ^ Fruhlinger, Josh (2019-09-25). "Social engineering explained: How criminals exploit human behavior". CSO Online.
{{cite web}}: CS1 maint: url-status (link) - ^ "What is Social Engineering? Examples and". www.webroot.com.
{{cite web}}: CS1 maint: url-status (link) - ^ a b c "Avoiding Social Engineering and Phishing Attacks | CISA". us-cert.cisa.gov.
{{cite web}}: CS1 maint: url-status (link) - ^ "What is Spear Phishing? - Definition". usa.kaspersky.com. 2021-01-13.
{{cite web}}: CS1 maint: url-status (link) - ^ a b Security, Mitnick. "6 Types of Social Engineering Attacks". www.mitnicksecurity.com.
{{cite web}}: CS1 maint: url-status (link) - ^ Fruhlinger, Josh (2019-05-17). "What is malware: Definition, examples, detection and recovery". CSO Online.
{{cite web}}: CS1 maint: url-status (link) - ^ Fruhlinger, Josh (2020-06-19). "Ransomware explained: How it works and how to remove it". CSO Online.
{{cite web}}: CS1 maint: url-status (link) - ^ "What is ransomware? | Techniques & Prevention | Terranova Security". terranovasecurity.com.
{{cite web}}: CS1 maint: url-status (link) - ^ Tasevski, Predrag (2016). "IT and Cyber Security Awareness – Raising Campaigns". Information & Security: An International Journal. 34 (1): 7–22. doi:10.11610/isij.3401.
- ^ a b c d e f g Wilson, M.; Hash, J. (2003). "NIST Special Publication 800-50: Computer Security" (PDF).
{{cite web}}: CS1 maint: url-status (link) - ^ a b c d e f g Employee Security Awareness Training
- ^ "Building a Security Awareness Program". www.gideonrasmussen.com.
{{cite web}}: CS1 maint: url-status (link) - ^ "Securely Using Mobile Apps - SANS OUCH! Newsletter - June 2021". www.sans.org.
{{cite web}}: CS1 maint: url-status (link) - ^ Forrest, Conner. "Ten best practices for securing the Internet of Things in your organization". ZDNet.
{{cite web}}: CS1 maint: url-status (link) - ^ a b c "Common Cyber Threats: Indicators and Countermeasures" (PDF).
{{cite web}}: CS1 maint: url-status (link) - ^ "Privacy - Protecting Your Digital Footprint - SANS OUCH! Newsletter - April 2021". www.sans.org.
{{cite web}}: CS1 maint: url-status (link)
